Hackers and cyber-attackers often exploit fear and chaotic conditions. The current COVID-19 pandemic is being used by hackers to launch many cunning Corona-related cyber-attacks.
These attacks may appear in emails as attachments or links, through phone calls from fake authorities, health services or system providers - such as Microsoft - or on websites you consider trustworthy.
As “home office” becomes the new standard for many of us, a lot of people are now working on less-secure network solutions.
To avoid being scammed, now is the time for you to brush up on cyber security standards and maintain a sceptical approach.
With the massive global demand for staying updated on the spread of the COVID-19 virus, a new risk arising is that of malicious websites acting as doppelganger versions of live mapping platforms. We have asked our trusted security risk partner NYA to take a closer look at this phenomenon, and to also share some general advice regarding increasing awareness and security given this challenging situation.
Context
On 10 March 2020, the US Department of Health’s Health Sector Cybersecurity Coordination Center (HC3) issued a cyber-security alert regarding malicious websites posing as the COVID-19 live mapping platform administrated by John Hopkins University’s Center for Systems Science and Engineering (CSSE). The computers of unsuspecting users were infected with a trojan malware . An investigation found this malware was a variation of the well-known AZORult family, an information-stealing malware often used by cyber criminals in theft operations involving social engineering and phishing techniques. It is believed the spread of the fake website was most likely through email attachments, advertisements and internet searches for the genuine CSSE dashboard.
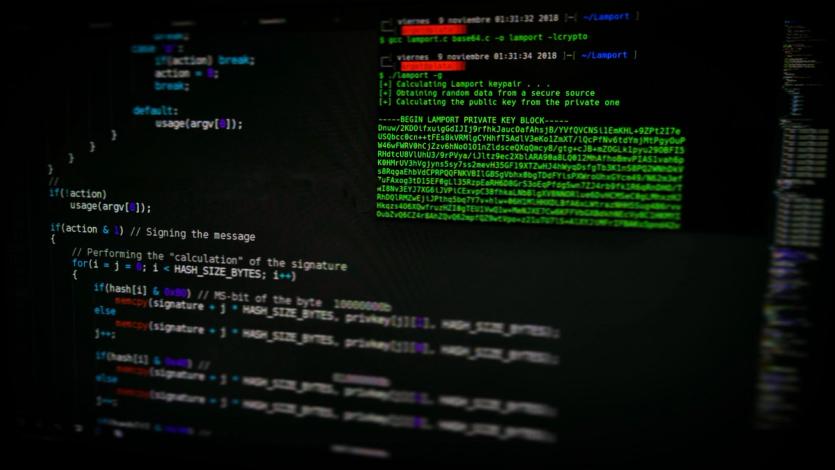
The AZORult Malware Family
AZORult was originally discovered in 2016; it has been linked to Russian underground forums and trading on the deep and dark webs. It originally had the ability to access and steal a user’s personal data including IP addresses, passwords, cookie preferences, credit card numbers and cryptocurrency account details, from their desktop computer/laptop. It could also install backdoor commands, enabling the further download of malware onto an infected machine. The latest version, AZORult++, which came to light in March 2019, added the lucrative ability to create a new administrator user on the victim’s device remotely, allowing the cyber attacker to enable Remote Desktop Protocol (RDP) functions without the victim’s knowledge .
Cyber criminals have seized upon recent public panic and the overwhelming need from both private and public sectors for the most up-to-date information and statistics regarding the global COVID-19 crisis. As the outbreak has become a pandemic, the demand for real-time information has grown exponentially and associated website, dashboard and app production has increased concurrently. As such, so too have malicious websites and phishing scams seeking to gain from acquiring a user’s personal information.
Advice
To help mitigate the threat posed by such malicious cyber activity, it is strongly advised that all internet users exhibit heightened vigilance in the content they access and share. This can be done by:
• Installing the most recent versions of industry-accredited security software
• Not opening email attachments from any source that is not immediately verifiable
• Only using the websites of established and reputable organisations/news media to obtain the latest information
• Alerting the IT department or provider if a malicious website or attachment has been clicked on, in order to initiate a damage limitation response
It should be noted that this specific malware is hidden in a file called ‘corna.exe’.
It is advised that:
• IT security teams include these indicators of compromise (IOC) to effectively quarantine malicious files and executables before they are able to run
• Regular security updates should be configured to run as such cases will to continue to rise and variants of the same malware are likely to be developed
• Network traffic should be monitored to identify when devices are communicating with command and control servers and disabled as soon as possible.
Limitation
NYA and Norwegian Hull Club’s opinion and advice are given on the basis of the information given to us in our instructions and the surrounding circumstances known to us to exist at the time when those instructions are given. We do not accept responsibility for verifying the information or investigating beyond its limits. Subsequent changes to relevant information or to the surrounding circumstances may affect the reliability of our opinion and advice but we do not accept responsibility for that effect. We do not accept responsibility for the outcome of action taken or not taken as a result of our opinion and advice, unless the possibility of that action being taken or not taken is set out in specific terms in our instructions.